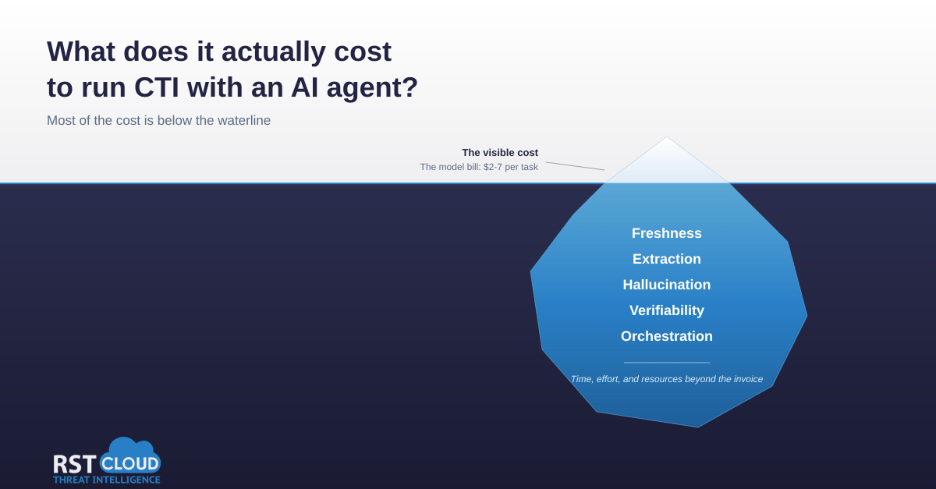
What does it actually cost to run CTI with an AI agent?
Modern deep research models can do real threat intelligence work. Before scaling that approach across a team, here is an honest accounting of the costs that don’t show up on the invoice. It is a fair question to ask in 2026. The frontier models are good. Deep research agents will autonomously plan a search, read […]
What does it actually cost to run CTI with an AI agent? Read More »