Future of Cyber Threats:
Wide ransomware attacks and usage of public online resources in cyberattacks (clouds, mobile apps, web)
The rise of destructive high-profile cyberattacks
The rise of APT groups and hack-and-leak attacks
Nanocore
Nanocore used by APT groups to target energy, aviation, and petrochemical production
Ransomware
Conti ransomware attack through targeted region phishing
Avos Locker
AvosLocker campaign
RAT
Spread of TigerRAT, NjRAT (also known as Bladabindi) etc
RST Threat Feed covers multiple IoCs types to detect and prevent all sorts of cyber attacks
| Description | Benefits | |
|---|---|---|
| IP Address Reputation | List of IP Addresses that are known to be used by cyber criminals (for example, C2 servers) | Gives undestanding if your networks are hacked already or not, detects participations of your assets in botnets, etc |
| Malicious Domains | A list of malicious Domains | Used to detect or prevent phishing, malware, data exfiltration, ransomware |
| Malicious URL | A list of malicious URLs | Detect or prevent actions to download malicious content or visit phishing resources |
| Malware File Hashes | List of malware files hashes (MD5, SHA1, SHA256) | Detect and prevent Ransomware, Trojans, Spyware, Keyloggers, RAT etc |
RST Threat Feed is a comprehensive and reliable source of information about cyber threats. Our threat intelligence platform collects data from a variety of sources, normalizes it, filters out irrelevant information, enriches it with additional context, and assigns a threat score to each piece of data. This allows our customers to quickly and easily access the most relevant and accurate information about potential cyber threats.
Threat intelligence, distributed at the level of legislation, is a world practice, and it is applied all over the world. This is a trend in the GCC region too. Development of actionable intelligence from the threats analysis, incident and vulnerability data, approved and required by such regulators as TRA and Central Bank of Bahrain, CITRA in the National Cyber Security Strategy of the State of Kuwait, Qatar National Center for Information Security, UAE Telecommunications Regulatory Authority, and others.
RST Cloud use a combination of numerous external sources and own proprietary methods to consistently and reliably collect indicators of compromises (IoC) and their context. This helps cybersecurity professionals more effectively assess the threat level of indicators and decide on appropriate courses of action quicker.
To help reduce the occurrence of false positives and false negatives, our verification engine filters out noise data that is not relevant to threat analysis. This helps to shorten investigation time and increase the efficiency of threat analysis by focusing on the most reliable and actionable indicators. By verifying the validity of IoCs, our verification process helps cybersecurity professionals more accurately assess the threat level of indicators and make more informed decisions about how to respond to potential threats.
Our threat feed is available through an API and has many pre-built integrations with popular security information and event management (SIEM), security orchestration, automation, and response (SOAR), next-generation firewall (NGFW), and threat intelligence platform (TIP) systems. This makes it easy for our customers to incorporate our threat data into their existing security infrastructure and workflows.
What makes us different
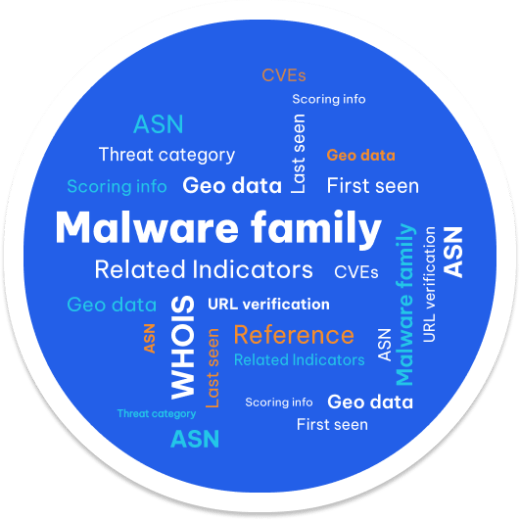
IoC normalisation, filtering and standardisation when collecting indicators
- data is normalised and is stored in one format
- all malware names are unified
- noise is filtered (MS Updates, CDPs, Well-known IPs, etc.)
Content enrichment
- all context data is parsed and normalised
- lots of additional enrichment mechanisms
- dedicated Whois API for domain data
Content and categorisation
- more than 20 malware categories
- Industry Tagging
- 250k+ unique indictors per day
- Related indicators and CVEs
- ASN (Org, Number of domains registered) and URL verification
- References to the sources and related indicators
Easy to use
- different integration options: Full database dump, API Lookup access, WHOIS API, special NGFW APIs
- Ready-to-use integration with popular SIEM/TIP/SOAR solutions
- a specialised download agent for smoothness integration
- out-of-the-box API for popular NGFW solutions
Integration
We provide quick and easy out-of-the-box integration with many SIEM, SOAR, TIP, EDR, XDR, NGFW, and WAF solutions. The knowledge we produce is actionable to the extent that machines can facilitate end-to-end detection, prevention, and response.
Fortigate firewalls can directly be integrated with RST Threat Feed via API. It gives options to block or alert on access to malicious websites or IP addresses. The integration is seamless and requires no extra software to be used to configure the firewalls.
Palo Alto NGFW can directly be integrated with RST Threat Feed via API. It gives options to block or alert on access to malicious websites or IP addresses. The integration is seamless and requires no extra software to be used to configure the firewalls.
RST Thread Feed integrated with IBM Qradar SIEM via RST Downloder agent. This agent automatically downloads all the required data and pushes it to the SIEM via API. There are options to filter indicators through its score and types, malware, tags etc
Palo Alto Cortex XSOAR can directly be integrated with RST Threat Feed via API. It gives an ability to query RST Cloud API directly from any playbook or using the war room commands.
RST Thread Feed integrated with Splunk. The app is published on the official Splunk marketplace and allows to automate downloading and maintenance of the feeds into Splunk.
RST Thread Feed is integrated with Microsoft Sentinel SIEM via a standard STIX/TAXII integration. There are options to filter indicators through its score and types, malware, tags etc
RST Thread Feed is integrated with Elastic SIEM solution via a custom elastic filebeat/agent configuration. There are options to filter indicators through its score and types, malware, tags etc
RST Thread Feed is integrated with MISP via a python script. There are options to filter indicators through its score and types, malware, tags etc
Cisco Firepower can directly be integrated with RST Threat Feed via API. It gives options to block or alert on access to malicious websites or IP addresses. The integration is seamless and requires no extra software to be used to configure the firewalls.
SAF Systems is a versatile platform for collecting and analysing machine data. It works in the fields of information security, IT infrastructure monitoring, and business process analysis. The integration of RST Threat Feed and RST Report Hub within the SAF platform empowers analysts to make informed decisions.