Insights into Phishing Trends and Tactics
Mar 28, 2023
Phishing remains one of the most significant threats to cybersecurity, as it continues to be a primary infiltration method in most cyber attacks. Numerous studies have highlighted the prevalence of phishing in data breaches, with Cisco’s 2021 Cybersecurity Threat Trends report revealing that 90% of data breaches involve phishing. Similarly, Symantec’s Internet Security Threat Report 2019 found that 65% of threat actors used spear phishing as the primary attack vector.
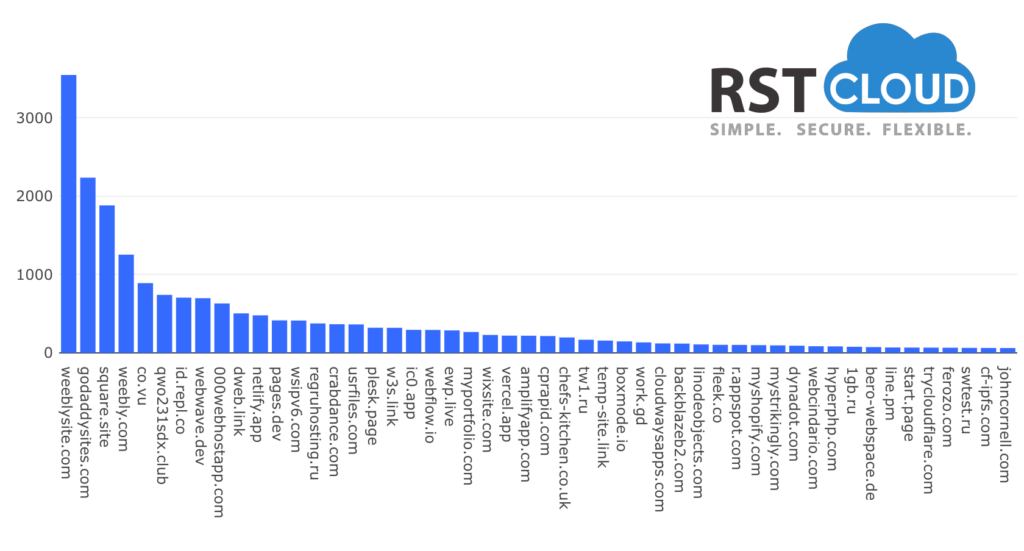
Recently, RST Cloud analysts studied the statistics for phishing indicators in our RST Threat Feed database over the past six months and identified some fundamental patterns. One of the most common phishing indicators is domains, which attackers often create for the sole purpose of phishing. These domains have a depth of one or two clicks, making them appear like a genuine resource.
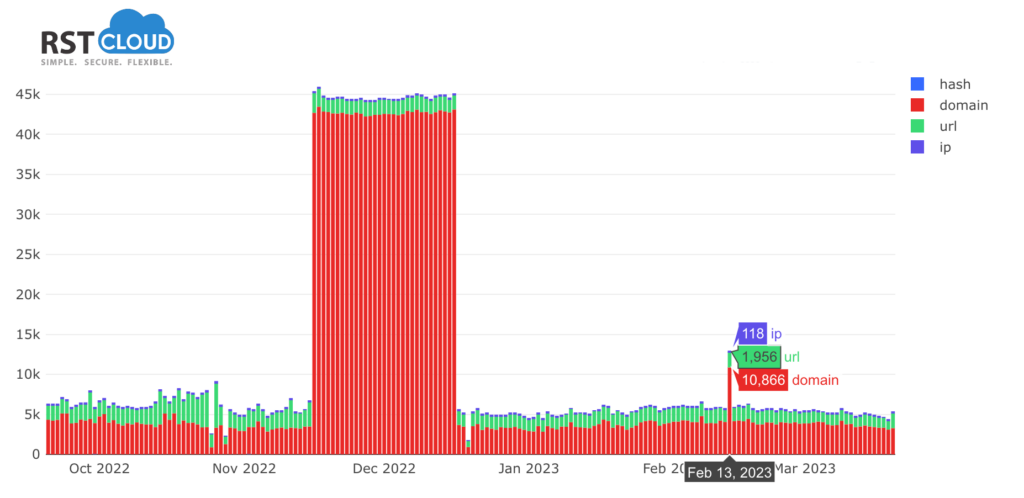
Another observation made by the analysts is that the number of phishing resources tends to increase dramatically on the eve of major holidays. In particular, the second half of December stands out as a period of increased phishing activity.
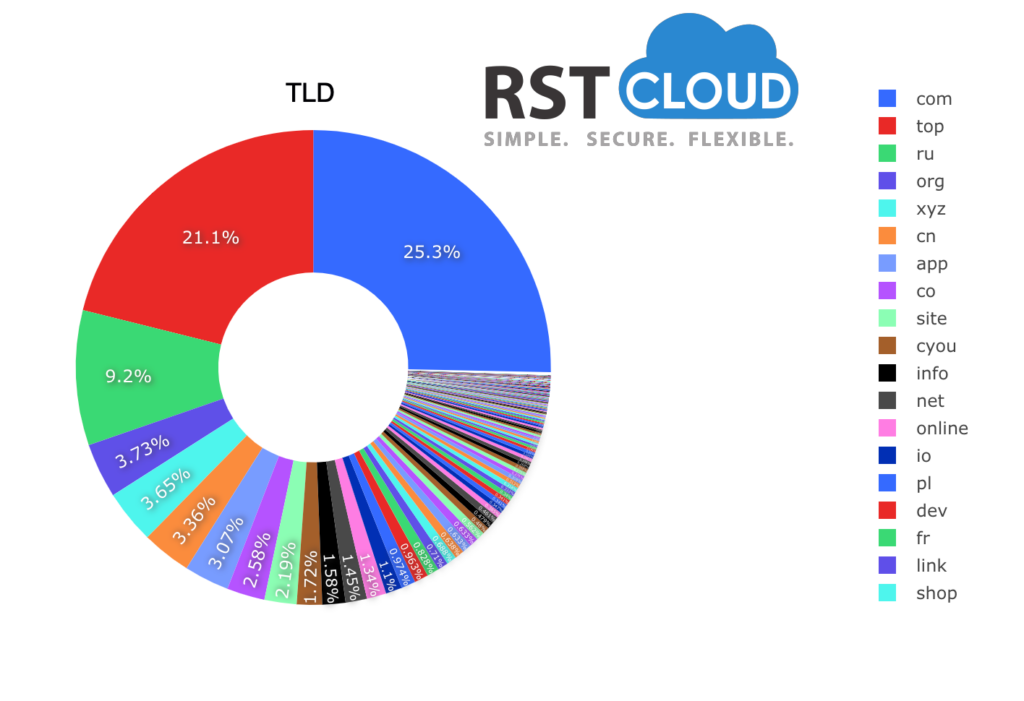
It’s also worth noting that the statistics by domains and Top-Level Domains (TLDs) are particularly interesting. The researchers found that attackers tend to use certain TLDs more frequently than others, with .com and .top being the most commonly used TLDs in phishing attacks.
So, what can we do to protect ourselves from phishing attacks? One of the most effective ways is to be vigilant and aware of the common tactics used by attackers. Be cautious of emails from unknown senders or messages that request personal information. Always verify the legitimacy of a website before entering sensitive information, and use multi-factor authentication whenever possible.
Phishing attacks may be becoming more sophisticated, but by staying alert and informed, we can protect ourselves and our data from harm. By staying up to date with the latest threat intelligence and incorporating it into their security strategies, individuals and organizations can better protect themselves from phishing attacks and other cyber threats.
You always can check a specific domain or URL on our IoC Lookup page.