8 Steps to normalise naming of cyber threats and related entities
Nov 21, 2022
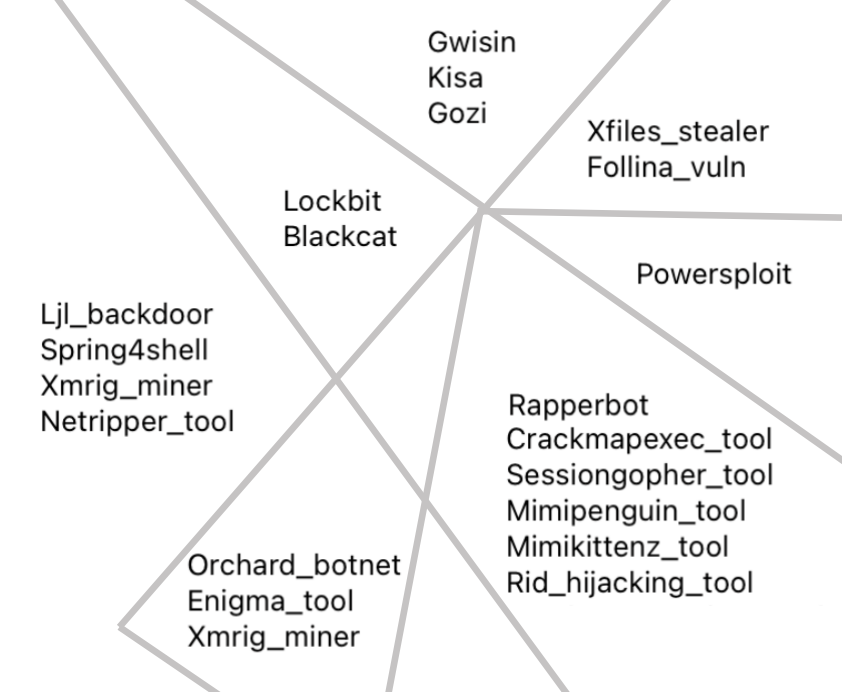
One of the challenging thing in IoC aggregation is to match all IoCs connected to one specific threat with each other due to different malware synonyms used by TI experts. Read about algorithm used by RST engine here: