Blog
Axios NPM Supply Chain Attack
RST CLOUD THREAT INTELLIGENCE _ TLP:CLEAR When the axios npm supply chain attack broke on 31 March 2026, twelve separate vendor reports followed within 48 hours. Elastic Security Labs, Google GTIG, Microsoft Threat Intelligence, Wiz, Snyk, StepSecurity, Tenable, and others each documented the campaign from a different vantage point: initial discovery, dropper mechanics, RAT architecture, attribution, remediation. Valuable, individually. But absorbing all twelve…
Your Threat Hunters Are Spending Their Day Reading Blogs. Here’s How to Fix That.
By Yury Sergeev and Juanita Koschier, RST Cloud Picture your best threat hunter. They came up through incident response, they think like an adversary, and they know your environment better than anyone. Now picture what they actually spent the first two hours of their day doing: reading threat reports, skimming vendor blogs, manually checking whether any of it is…
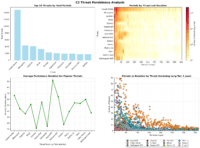
C2 Tracking Approaches: From Search Engines to Managed Feeds
Command and Control (C2) infrastructure tracking is a cornerstone of modern cyber threat intelligence (CTI). By identifying and monitoring attacker-controlled servers, defenders can block malicious communications, detect intrusions earlier, and ultimately reduce the dwell time of threats within their environments. With so many platforms and techniques available, each offering unique strengths, how can CTI teams,…