
Axios NPM Supply Chain Attack
Apr 8, 2026
RST CLOUD THREAT INTELLIGENCE _ TLP:CLEAR
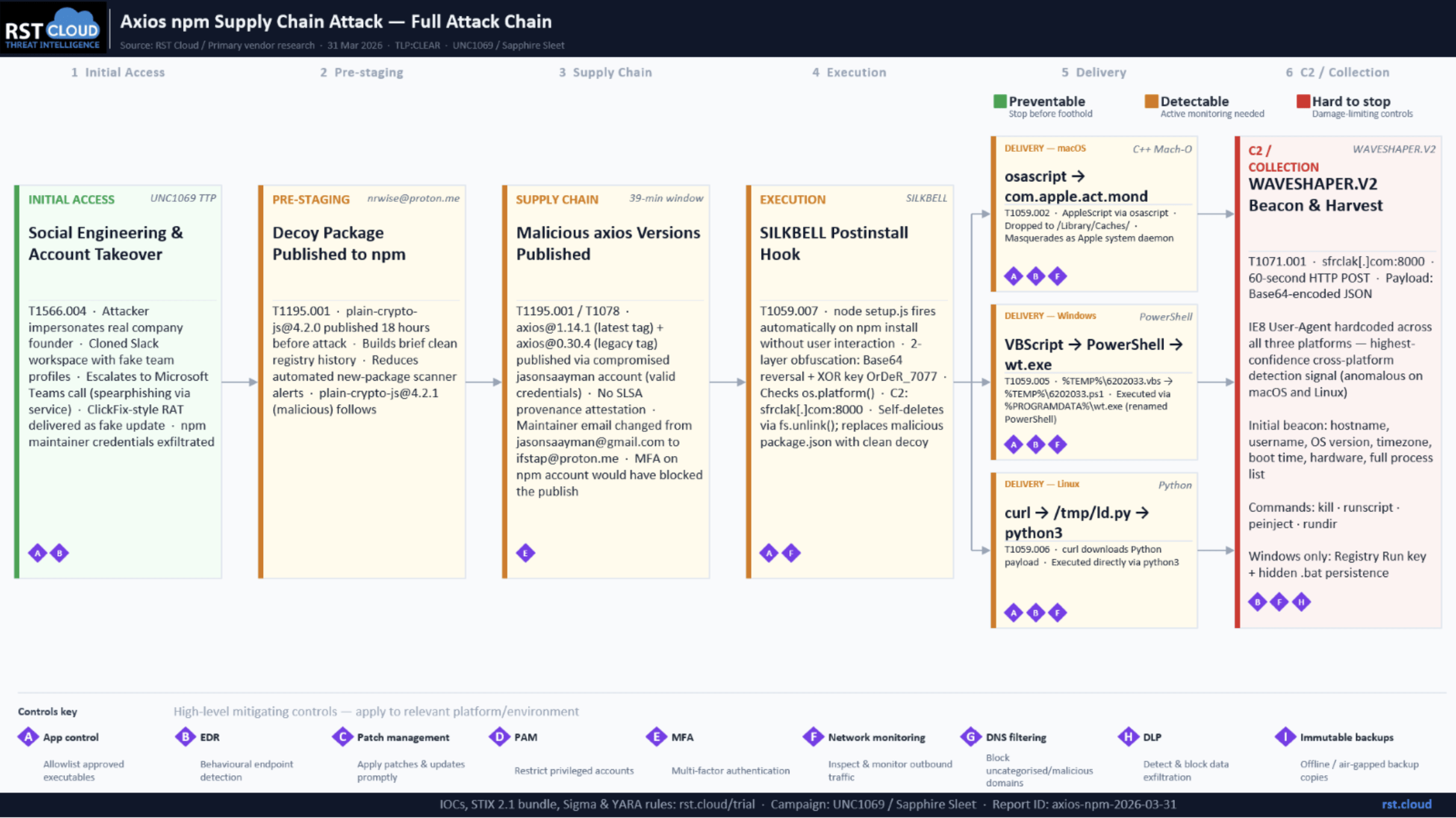
When the axios npm supply chain attack broke on 31 March 2026, twelve separate vendor reports followed within 48 hours. Elastic Security Labs, Google GTIG, Microsoft Threat Intelligence, Wiz, Snyk, StepSecurity, Tenable, and others each documented the campaign from a different vantage point: initial discovery, dropper mechanics, RAT architecture, attribution, remediation. Valuable, individually. But absorbing all twelve takes hours that most CTI teams do not have in the middle of an active incident response.
Cross-source analysis changes what is visible. Any single report captures one vantage point: the vendor who found it first, the tooling they had, the infrastructure they could see. What follows is what the full corpus produces when analysed together: the full attack chain from initial social engineering through npm registry compromise, converging attribution from two independent vendors, formal malware naming, and detection artifacts derived from the aggregate picture rather than any single source. Some of this intelligence does not exist in any one report. It emerges from the correlation.

The Campaign in Brief
On 31 March 2026, two malicious versions of the axios JavaScript HTTP client (1.14.1 and 0.30.4) were published to the npm registry via a compromised maintainer account. Both contained a hidden dependency, plain-crypto-js@4.2.1, whose postinstall hook silently downloaded and executed a cross-platform remote access trojan on any machine that ran npm install during the exposure window. The malicious versions were live for approximately three hours (00:21 to approximately 03:15–03:20 UTC) before being removed. With approximately 100 million weekly downloads on the 1.x branch and 83 million on the 0.x branch, per GTIG, even a three-hour exposure window represents significant potential reach. Wiz observed RAT execution in approximately 3% of affected environments.
Two major threat intelligence vendors have independently attributed the campaign to North Korean state-sponsored actors: Google Threat Intelligence Group (GTIG) tracks the responsible cluster as UNC1069; Microsoft Threat Intelligence tracks the same infrastructure and campaign as Sapphire Sleet. Microsoft notes that Sapphire Sleet overlaps with designations used by other vendors including UNC1069, STARDUST CHOLLIMA, Alluring Pisces, BlueNoroff, CageyChameleon, and CryptoCore. Both attributions converge on the same actor.
What RST Report Hub Ingested
RST Report Hub processed eight primary vendor analyses on this campaign: Elastic Security Labs, Google GTIG, Microsoft Security Blog, Wiz, Snyk, StepSecurity, Tenable, and NVISO. The campaign object was available in our threat intelligence platform by 18:43 UTC on 31 March 2026, approximately 18 hours after the malicious packages were published and while the incident was still being actively investigated across the industry. Cross-source correlation of the SILKBELL dropper name, WAVESHAPER.V2 lineage, and dual attribution (UNC1069/Sapphire Sleet) completed as the major vendor analyses landed on 3–4 April.
Account Takeover: How the Chain Began
The npm registry compromise was not the starting point. In his post-mortem published on 2 April 2026 on the axios GitHub repository, lead maintainer Jason Saayman documented how his credentials were taken approximately two weeks before the malicious packages appeared.
The operation followed a social engineering playbook consistent with UNC1069’s documented targeting of high-value individuals in the cryptocurrency and open-source ecosystems. The attacker impersonated the founder of a real company, cloning both the founder’s identity and the company’s branding. Saayman was invited into a genuine Slack workspace that had been built to pass as the company’s internal environment: channels sharing LinkedIn posts linking to the real company’s account, fake profiles for employees, and accounts posing as other open-source maintainers. The workspace was, in Saayman’s words, “thought out very well.”
The interaction then moved to Microsoft Teams, staged to appear as a multi-participant call. During it, Saayman was told something on his system was out of date. He installed what he believed was an update. That was the RAT. Once deployed on his machine, it gave the attacker access to the npm account credentials used to publish the malicious axios releases.
The post-mortem notes that at no point was there an automated mechanism that would have detected an unauthorised publish. The attack exploited both the human and the workflow gap simultaneously.
Attack Timeline
| Time (UTC) | Event |
| 30 March, 05:57 | plain-crypto-js@4.2.0 published by nrwise@proton.me — clean decoy to build registry history |
| 30 March, 23:59 | plain-crypto-js@4.2.1 published by nrwise@proton.me — malicious payload |
| 31 March, 00:21 | axios@1.14.1 published via compromised jasonsaayman account, tagged latest |
| 31 March, 01:00 | axios@0.30.4 published via compromised jasonsaayman account, tagged legacy |
| ~03:15–03:20 | Malicious versions removed from npm registry |
The shift from legitimate to malicious publishing is forensically visible in the npm registry metadata. Prior legitimate releases were published via GitHub Actions OIDC with SLSA provenance attestations. The malicious versions were direct CLI publishes with no provenance, and the maintainer email had been changed from jasonsaayman@gmail.com to ifstap@proton.me.
The Dropper: SILKBELL
GTIG tracks the setup.js postinstall script as SILKBELL. It is the operational core of the delivery chain: a Node.js file that executes automatically during npm install without any user interaction.
SILKBELL uses two-layer obfuscation to conceal its behaviour. All critical strings, module names, URLs, and shell commands are stored in an encoded array decoded at runtime. Layer one applies string reversal and Base64 decoding; layer two applies an XOR cipher using the key OrDeR_7077 with a position-dependent index.
After decoding, SILKBELL checks os.platform() and sends an HTTP POST to http://sfrclak[.]com:8000/6202033 with a platform-specific body: packages.npm.org/product0 (macOS), packages.npm.org/product1 (Windows), or packages.npm.org/product2 (Linux). The packages.npm.org/ prefix is deliberate: it makes the outbound request resemble legitimate npm registry traffic in network logs.
Once the stage-2 payload is delivered, SILKBELL self-deletes via fs.unlink(__filename) and replaces the malicious package.json with a clean decoy, erasing all evidence of the postinstall hook from node_modules. Post-incident inspection of the directory reveals nothing suspicious. Only lockfiles and npm audit logs retain forensic evidence.
The platform-specific delivery paths:
- macOS: AppleScript via osascript downloads the payload to /Library/Caches/com.apple.act.mond, masquerading as an Apple system daemon.
- Windows: VBScript downloads a PowerShell script to %TEMP%\6202033.ps1 and executes it via a renamed PowerShell binary at %PROGRAMDATA%\wt.exe, masquerading as Windows Terminal.
- Linux: curl downloads a Python script to /tmp/ld.py and executes it via python3.
The Payload: WAVESHAPER.V2
GTIG tracks the stage-2 payloads as WAVESHAPER.V2, an updated version of WAVESHAPER, a macOS and Linux backdoor previously attributed to UNC1069. The C++ Mach-O binary is the most directly linked variant; Elastic Security Labs identified significant code overlap with prior WAVESHAPER samples, and GTIG’s attribution rests partly on this malware lineage alongside infrastructure overlaps.
What makes the payload architecture operationally notable is that the three platform implementations (PowerShell for Windows, C++ for macOS, Python for Linux) are not three separate tools. They share an identical C2 protocol, command vocabulary, beacon interval, session identifier format, and hardcoded User-Agent string. This is a single cross-platform implant specification with platform-native implementations, indicating a well-resourced, well-coordinated team working from a shared design document.
All three variants beacon to sfrclak[.]com:8000 every 60 seconds via HTTP POST, with payloads encoded as Base64-encoded JSON. The User-Agent hardcoded across all three is: mozilla/4.0 (compatible; msie 8.0; windows nt 5.1; trident/4.0).
This is the IE8/Windows XP User-Agent string. It is anachronistic on any modern system and is particularly anomalous on macOS and Linux, where it has no plausible legitimate explanation. It is the single most reliable cross-platform detection indicator for this campaign, requiring no domain blocklist refresh and visible in any network log that captures HTTP headers.
On initialisation, each variant sends an initial system profile beacon containing hostname, username, OS version, timezone, boot time, install date, hardware model, CPU type, and full process list, followed by periodic lightweight keepalives. The C2 command set is consistent across all three: kill (self-terminate), runscript (execute operator-supplied code), peinject (drop and execute a binary payload), and rundir (enumerate a filesystem path). The Windows variant adds persistence via a Registry Run key and hidden batch file; the macOS and Linux variants have no persistence.
Attribution
Both GTIG and Microsoft Threat Intelligence have independently attributed this campaign to North Korean state actors, using different cluster names for the same underlying actor.
GTIG / UNC1069: Attribution rests on two pillars. First, malware lineage: WAVESHAPER.V2 is a direct evolution of WAVESHAPER, sharing identical C2 polling behaviour, the same anachronistic User-Agent string, and identical temporary staging directories on macOS. Second, infrastructure overlap: the C2 domain sfrclak[.]com (resolving to 142.11.206[.]73) was traced to connections from an AstrillVPN node previously used by UNC1069, with adjacent infrastructure on the same ASN historically linked to the group. GTIG describes UNC1069 as active since at least 2018 and primarily focused on cryptocurrency theft. RST assesses that the observed collection targets in this campaign — cloud credentials, SSH keys, CI/CD tokens, and npm account credentials — are consistent with access accumulation for downstream operations, which may include both cryptocurrency theft and longer-term access brokerage.
Microsoft / Sapphire Sleet: Microsoft Threat Intelligence linked the same C2 infrastructure and plain-crypto-js account to Sapphire Sleet. Per the Microsoft Security Blog, Sapphire Sleet overlaps with designations used by other vendors including UNC1069, STARDUST CHOLLIMA, Alluring Pisces, BlueNoroff, CageyChameleon, and CryptoCore.
On cross-vendor alignment: GTIG analyst John Hultquist noted that several DPRK threat actors have a history of supply chain compromises and malicious npm packages, characterising this as consistent with broader North Korean tradecraft. The use of an npm supply chain vector by UNC1069 specifically represents an escalation for this cluster, not an established pattern from the group alone.
The axios campaign occurred within two weeks of a separate supply chain operation by UNC6780 (TeamPCP) targeting Trivy, Checkmarx, LiteLLM, and Telnyx between 19–27 March 2026. GTIG has explicitly assessed the axios campaign as a separate operation by a distinct threat actor.
RST Cloud tracks this campaign under dual attribution: UNC1069 (GTIG) / Sapphire Sleet (Microsoft), with high confidence North Korean nexus.
Indicators of Compromise
All indicators below are corroborated across multiple primary sources (GTIG, Elastic Security Labs, Microsoft, Wiz, StepSecurity).
| Indicator | Type | Description |
| sfrclak[.]com | Domain | C2 (all platforms, port 8000) |
| 142.11.206[.]73 | IP | C2 server IP |
| mozilla/4.0 (compatible; msie 8.0; windows nt 5.1; trident/4.0) | User-Agent | Hardcoded across all WAVESHAPER.V2 variants |
| 617b67a8e1210e4fc87c92d1d1da45a2f311c08d26e89b12307cf583c900d101 | SHA-256 | Windows RAT: 6202033.ps1 |
| 92ff08773995ebc8d55ec4b8e1a225d0d1e51efa4ef88b8849d0071230c9645a | SHA-256 | macOS RAT: com.apple.act.mond |
| fcb81618bb15edfdedfb638b4c08a2af9cac9ecfa551af135a8402bf980375cf | SHA-256 | Linux RAT: ld.py |
| axios@1.14.1 | npm | Malicious – do not install |
| axios@0.30.4 | npm | Malicious – do not install |
| plain-crypto-js@4.2.1 | npm | SILKBELL dropper delivery vehicle |
| ifstap@proton.me | Attacker-controlled axios maintainer email | |
| nrwise@proton.me | plain-crypto-js publisher email |
Detection
The most reliable immediate detection indicators are network-layer. Any outbound connection to sfrclak[.]com or 142.11.206[.]73 should be treated as a confirmed compromise indicator. Any HTTP POST using the IE8 User-Agent on a modern host is high-confidence malicious activity; the rule requires no domain or IP blocklist refresh and is particularly strong on macOS and Linux.
For host-based detection:
- /Library/Caches/com.apple.act.mond created by curl, osascript, or node (macOS)
- %PROGRAMDATA%\wt.exe execution with -NoProfile or -ep Bypass (Windows)
- %TEMP%\6202033.vbs file creation — VBScript stager, intermediate step in Windows execution chain
- %TEMP%\6202033.ps1 file creation (Windows)
- /tmp/ld.py creation, or hidden files matching /tmp/\.[a-zA-Z0-9]{6} created by python or node (Linux)
- Node.js spawning curl, python3, or osascript during npm install (all platforms)
RST Cloud has published a STIX 2.1 bundle, seven Sigma rules, and six YARA rules for this campaign. The STIX bundle covers the full object graph: dual-attributed threat actor, campaign, four malware objects (SILKBELL dropper and three WAVESHAPER.V2 variants), six indicators, eight ATT&CK-mapped attack patterns, and the relationships connecting them.
Remediation
Pin to axios@1.14.0 (last legitimate 1.x release with SLSA provenance) or axios@0.30.3 for the 0.x branch. Inspect all lockfiles for plain-crypto-js at any version and remove it. When reinstalling packages on affected systems, use npm ci –ignore-scripts to prevent postinstall hooks from executing during the cleanup process. Clear npm, yarn, and pnpm caches on all workstations and build servers.
If execution of the malicious versions is confirmed or cannot be ruled out, rotate all credentials, API keys, SSH keys, and cloud tokens accessible from the affected environment. Review CI/CD pipeline logs for outbound connections to sfrclak[.]com:8000 between 00:21 and 03:20 UTC on 31 March 2026. Block all traffic to sfrclak[.]com and 142.11.206[.]73 at the perimeter.
What Cross-Source Correlation Produced
The dual attribution picture in this post — UNC1069 confirmed by GTIG, Sapphire Sleet confirmed by Microsoft, converging on the same infrastructure — is not present in any single vendor report. GTIG does not surface the Microsoft attribution. Microsoft does not provide the WAVESHAPER.V2 malware lineage that grounds GTIG’s confidence assessment. The complete picture requires reading both, and mapping them against each other.
This is what cross-source correlation produces that individual reports cannot: intelligence that exists in the gaps between sources, not within any one of them. The axios campaign generated eight substantive vendor analyses within 48 hours. Each was valuable. None was sufficient alone.
RST Report Hub ingested those reports as they were published and correlated them into the structured product above. The STIX bundle, detection rules, and IOC table reflect the aggregated picture.
Download the detection artifacts
- STIX 2.1 Bundle (axios-sca-bundle.json) — 37 objects including SILKBELL, WAVESHAPER.V2, dual attribution
- Sigma Rules (axios-sca-detections.yml) — 7 rules across network, process, and file event sources
- YARA Rules (axios-sca.yar) — 6 rules, compiled and validated
For access to this layer of cross-source correlation across all campaigns: rst.cloud trial request
All technical claims are sourced from published primary research. References: Elastic Security Labs · Google GTIG · Microsoft Security Blog · Wiz · Snyk · StepSecurity · Tenable · NVISO